The CEO was understandably upset. Hackers had invaded his company’s computer network, inserting a story on top of the company website calling him a moron who was “driving the entire company into the ground.”
The CEO demanded to know: What was his IT team going to do about it?
Mariah Kenny, a third-year University of Virginia computer science student, had some explaining to do. Kenny is captain of the UVA Cyber Defense team, a student team that posed as information security professionals defending their mock company and its play-acting CEO against a barrage of vicious cyberattacks during the Mid-Atlantic Collegiate Cyber Defense Competition, held March 16 and 17 at Johns Hopkins University.
Though it was their first time competing, the UVA students performed well enough to defeat seven other teams and earn a place at next month’s National Collegiate Cyber Defense Competition in Orlando, Florida. In the process, they bested defending national champion University of Maryland, Baltimore County – one day after another UVA team was disappointed in its NCAA Tournament matchup with UMBC.
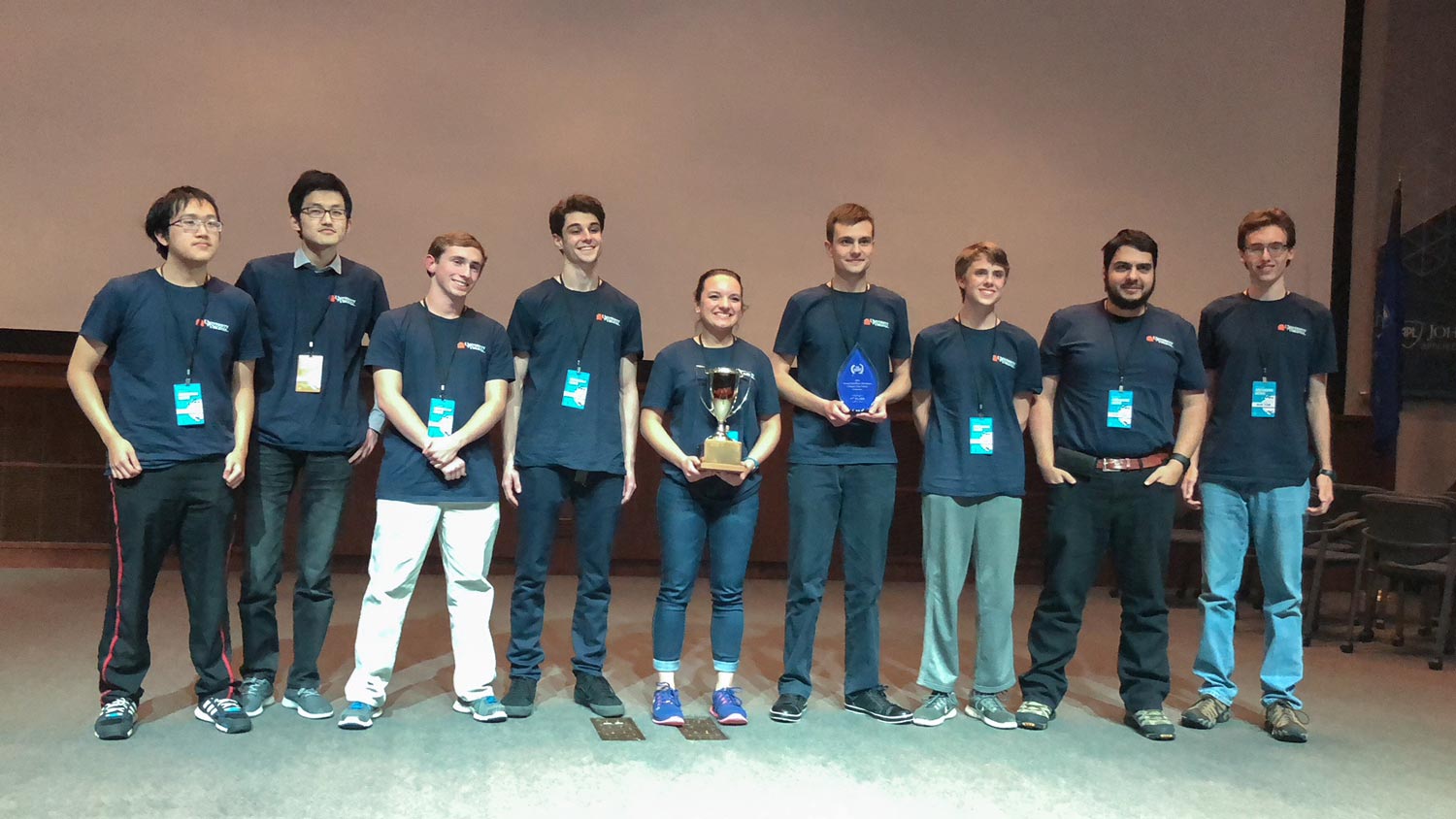
Mariah Kenny, center, led the UVA team to an upset of defending national champion UMBC and a berth in the national cybersecurity competition. (Photo courtesy School of Engineering and Applied Science)
“In order to win, we had to show we could maintain business continuity while defending against professional hackers,” Kenny said. The competition was designed to simulate real-life conditions in which companies employ both “blue teams” – security professionals responsible for thwarting system abuses or outright attacks – and “red teams” of trained hackers who seek to exploit vulnerabilities and gain unauthorized access.
UVA and the other schools were blue teams, and industry professionals posed as the red teams. The students were assigned to defend a company that owned and operated various online news sites – an industry that has been under scrutiny in real life for its reported susceptibility to hacking.
The UVA team was responsible for the security of its company’s full network, including all servers and software, while the hackers tried to wreak havoc.
Kenny, as the team captain, was required to stay in communication with the competition official posing as the chief executive officer. She had to clearly explain the cybersecurity risks and what the UVA team was doing to resolve the issues.
“We had a pretty solid game plan,” Kenny said. “We split into different groups. We had a Windows group, a firewall group, a Linux group, and so on. Each group knew which systems they were in charge of, and they had an explicit list of tasks.
“Unlike other teams, we didn’t focus too much in one category, because they all mattered. We focused on all of them. And we were in constant communication.”
Each time the team identified a security breach, they filled out an incident report form mimicking one used by the U.S. Secret Service, Kenny said. On the form, they had to explain the breach, what the hackers did, the effects on the business and how the team corrected the problem.
Teams were evaluated in six categories, Kenny said: their ability to keep the company’s critical services running; the clarity of their communication with the CEO; how they handled different business tasks tossed at them during the competition; how they maintained customers’ access to the mock company’s websites even during cyberattacks; the teams’ skill at identifying malware installed in their systems; and the quality of their incident reports.
“We just knew our priorities,” Kenny said. “If one system went down, we didn’t put all of our resources into that. We kept people working in their assigned areas knowing that all of them were important.”
Things occasionally got tense.
The red team hacked into the security cameras in the competition rooms, grabbed pictures of the UVA team working and then e-mailed the photos to them. At one point, the attackers just started shutting down the team’s computers. Every time UVA would restart the machines, the hackers would shut them down again.
And then there was the calling-the-CEO-a-moron incident.
“It was stressful,” Kenny said. “But everybody had fun. It was great practice, and we learned a lot.”
Ahmed Ibrahim, assistant professor of computer science and the team’s adviser, said the competition was an invaluable lesson for the students. First-year students Roman Bohuk and Jake Smith, who are also co-presidents of UVA’s Computer and Network Security Club, brought the team together. Besides Bohuk, Smith and Kenny, the team includes graduate student Abbas Naderi Afooshteh, fourth-year student Paul Sanders, third-year Jibang Wu, second-year Quintin DeGroot and first-years Daniel Chen and Calvin Krist. All are computer science students; Sanders has a double major in math.
Ibrahim, who teaches network security, pursues opportunities for his students to experience real-world cybersecurity challenges. He has partnered with Facebook and CodePath.org to give students hands-on training in cybersecurity threats. His work led to Kenny and another student earning Facebook scholarships to the Women in Cybersecurity conference in Chicago, being held this weekend.

The competition, presented by the National Science Foundation’s National Cyberwatch Center and defense contractor Raytheon, is another opportunity for students to practice the skills they will need if they are to succeed as cybersecurity professionals.
“Companies want people who know the fundamentals and have very good technical skills, but who also are great communicators,” Ibrahim said.
“It’s remarkable that UVA won this competition in the team’s first year,” said Kevin Skadron, who chairs the Department of Computer Science in UVA’s School of Engineering & Applied Science. “The students did an outstanding job. I also give a tremendous amount of credit to Professor Ibrahim for getting UVA involved in this competition, and for all his other efforts to create opportunities for our students to get involved in cybersecurity activities, gain experience and build confidence.
“These activities demonstrate UVA’s commitment to preparing the cybersecurity leaders of the future, and that is a critical contribution to the economy of the Commonwealth of Virginia and the United States.”
For now, the UVA Cyber Defense team will continue planning its strategy for the national competition, practicing defensive maneuvers and looking for students who might want to join the Computer and Network Security Club.
“We’re always looking for new members,” Smith said. “We’re happy to teach anyone we can to get them involved in the cybersecurity community.”
Media Contact
Article Information
March 23, 2018
/content/uva-knocks-defending-champ-umbc-reach-national-cybersecurity-competition

